ISO IEC 10118-2-2010 pdf download
ISO IEC 10118-2-2010 pdf download Information technology — Security techniques — Hash-functions — Part 2: Hash-functions using an n-bit block cipher
6.6 Output transformation The output transformation T is simply truncation, i.e., the hash-code H is derived by taking the leftmost L H bits of the final output block H q .
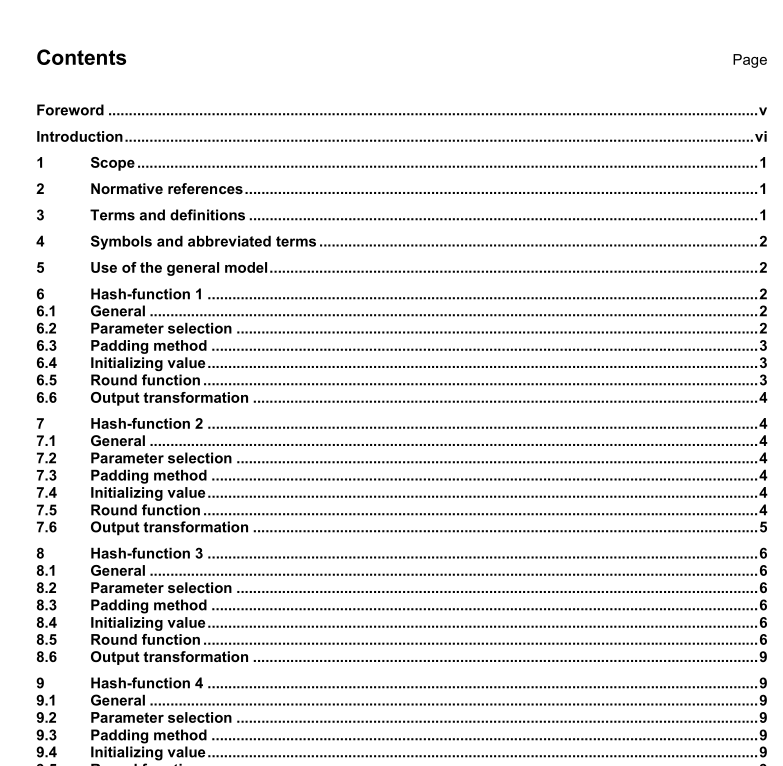
7 Hash-function 2
7.1 General The hash-function specified in this clause provides hash-codes of length L 1 and L 2 where L 1 is equal to n and L 2 is equal to 2n. Some specific definitions that are required to specify hash-function 2 follow.
NOTE 1 This hash-function is described in [4].
NOTE 2 In [6], theoretical attacks on hash-function 2 have been reported: a collision attack, with n = 128, which has complexity 2 124.5 , and a preimage attack requiring complexity and space about 2 n . The only reason to keep hash-function 2 in this part of ISO/IEC 10118 is for compatibility with the existing applications.
7.2 Parameter selection The parameters L 1 , L 2 and L H for the hash-function specified in this clause shall satisfy L 1 = n, L 2 = 2n, and L H is less than or equal to 2n.
7.3 Padding method The selection of the padding method for use with this hash-function is beyond the scope of this part of ISO/IEC 10118. As minimum requirements, the padding method shall output a set of q blocks D 1 , D 2 , …, D q where each block D j is of length n and shall be such that each possible input produces distinct outputs. Examples of padding methods are presented in ISO/IEC 10118-1:2000, Annex A.
7.4 Initializing value The selection of the IV (of length 2n) for use with this hash-function is beyond the scope of this part of ISO/IEC 10118. The IV shall be a bit-string of length 2n and the value of the IV shall be agreed upon and fixed by users of the hash-function. However, the IV shall be selected such that u(IV L ) and u’ (IV R ) are different.
7.5 Round function The round function φ combines a padded data block D j (of L 1 = n bits) with H j-1 , the previous output of the round function (of L 2 = 2n bits), to yield H j . As part of the round function it is necessary to choose two transformations u and u’. These transformations are used to transform an output block into two suitable L K bit keys for the algorithm E. The specification of u and u’ is beyond the scope of this part of ISO/IEC 10118. However, it should be taken into consideration that the selection of u and u’ is important for the security of the hash-function.